Promoter Éliennes de l'Érable rejected the class action request, demanding nearly $1 million in court costs from the citizens of...
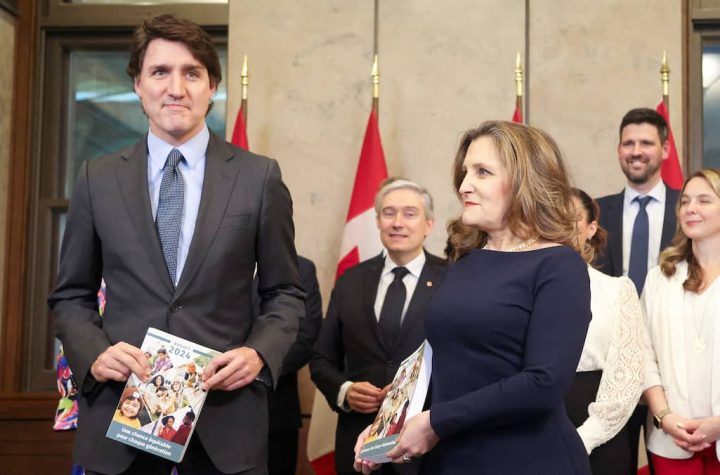
The Federation Council has serious objections to the Freeland budget presented this week.In a letter sent to Justin Trudeau on...
It is not serious. Once again this year, Tim Hortons is telling customers they've won a top prize in the...
A young Montreal patient has never forgotten her recent visit to the emergency room, when she found herself alone in...
Tuesday's budget was seen as an opportunity for Justin Trudeau's Liberals to return to political glory. However, it was a...
Asian cuisine fans, I have a new brand for you to discover in Montcalm, serving brunches and Japanese-inspired dishes. The...
CBC/Radio-Canada will cut fewer positions than expected this year, thanks in particular to new state funding, management announced Wednesday in...
(NEW YORK) Car maker Tesla will once again present to its shareholders, at its next general meeting in June, its...
Six years ago, Simon bought a mobile canteen for $110,000 and his father agreed to act as guarantor for the...
Names, first names, contact details, information on banking products... Around ten customers of the National Bank (BN) were "affected by...